Authentication Failed: Please Try Again Later or Use Public Search Instead.
- Details
- Reviews
- Installation
- Back up
- Evolution
Secure WordPress login with this 2 factor authentication (TFA / 2FA) plugin. Users for whom it is enabled will crave a one-fourth dimension code in social club to log in. From the authors of UpdraftPlus – WP'south #1 fill-in/restore plugin, with over two meg active installs.
Are you completely new to TFA? If so, please see our FAQ.
Features (please see the "Screenshots" for more data):
- Supports standard TOTP + HOTP protocols (and and so supports Google Authenticator, Authy, and many others).
- Displays graphical QR codes for easy scanning into apps on your phone/tablet
- TFA can be fabricated available on a per-role basis (e.g. available for admins, but not for subscribers)
- TFA can be turned on or off by each user
- TFA can be required for specified user levels, after a defined fourth dimension flow (eastward.g. crave all admins to have TFA, once their accounts are a calendar week former) (Premium version), including forcing them to immediately prepare up (by redirecting them to the page to do so)
- Supports front end-end editing of settings, via [twofactor_user_settings] shortcode (i.e. users don't need access to the WP dashboard). (The Premium version allows custom designing of any layout y'all wish).
- Site owners can allow "trusted devices" on which TFA codes are only asked for a chosen number of days (instead of every login); e.g. thirty days (Premium version)
- Works together with "Theme My Login" (both forms and widgets)
- Includes support for the WooCommerce and Affiliates-WP login forms
- Includes support for Elementor Pro login forms (Premium version)
- Includes support for bbPress login forms (Premium version)
- Includes support for any and every third-party login class (Premium version) without any farther coding needed via appending your TFA lawmaking to the end of your password
- Does non mention or request second factor until the user has been identified as i with TFA enabled (i.e. nix is shown to users who do not have it enabled)
- WP Multisite compatible (plugin should be network activated)
- Simplified user interface and code base for ease of use and performance
- Added a number of actress security checks to the original forked code
- Emergency codes for when you lose your phone/tablet (Premium version)
- When using the front-stop shortcode (Premium version), require the user to enter the current TFA code correctly to be able to activate TFA
- Works together with "WP Members" (shortcode form)
- Administrators tin can access other users' codes, and turn them on/off when needed (Premium version)
Why use TFA / 2FA ?
Read this! https://www.wired.com/2012/08/apple-amazon-mat-honan-hacking/
How Does TFA / 2FA Work?
This plugin uses the industry standard TFA / 2FA algorithm TOTP or HOTP for creating One Time Passwords. These are used past Google Authenticator, Authy, and many other OTP applications that you can deploy on your phone etc.
A TOTP code is valid for a certain fourth dimension. Whatever plan you utilise (i.eastward. Google Authenticator, etc.) volition show a different code every so frequently.
Plugin Notes
This plugin began life in early on 2022 equally a friendly fork and enhancement of Oscar Hane'southward "two factor auth" plugin.
-
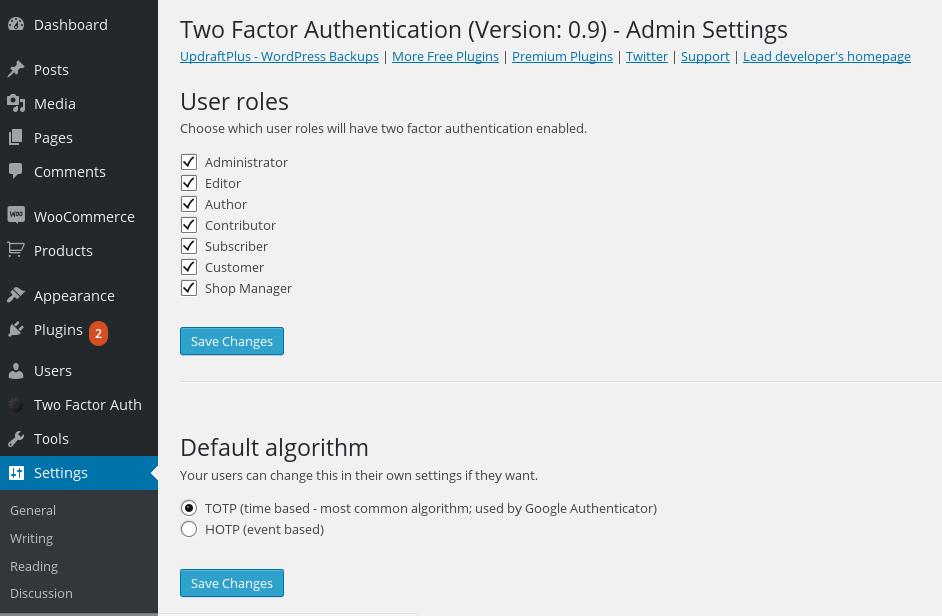
Site-wide settings
-

User settings (dashboard)
-

User settings (front-end, via shortcode)
-
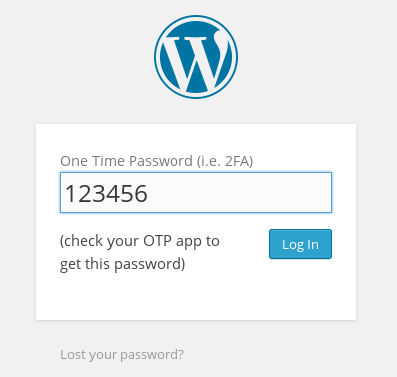
Regular WP login class requesting OTP code (afterward successful username/password entry)
-
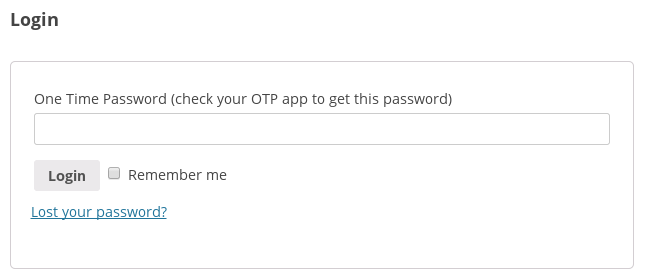
WooCommerce login course requesting OTP code (later successful username/password entry)
-

What the user sees if opening a wrong OTP code on the regular WP login form
-

What the user sees if opening a wrong OTP code on the WooCommerce login course
-
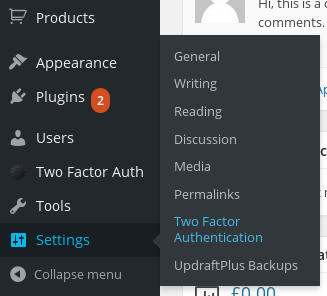
Where to discover the site-broad settings in the dashboard carte
-
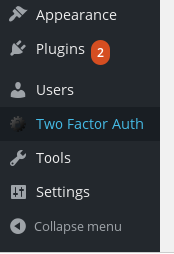
Where to find the user's personal settings in the dashboard bill of fare
-
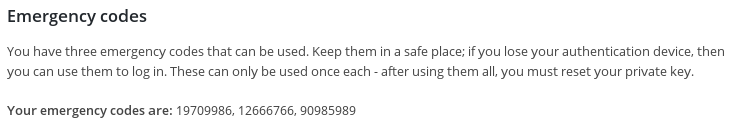
Emergency codes (Premium version)
-
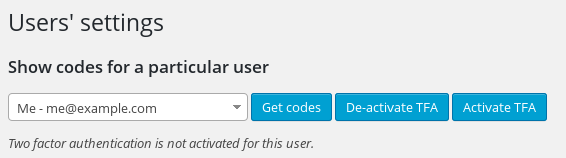
Adjusting other users' settings as an admin (Premium version)
-

Building your own design for the folio with custom curt-codes (Premium version)
This plugin requires PHP version 5.3 or higher and back up for either php-openssl or PHP mcrypt. The vast majority of PHP setups will have one of these. If not, ask your hosting visitor.
- Search for 'Two Factor Authentication' in the 'Plugins' carte du jour in WordPress.
- Click the 'Install' button. (Brand certain yous picks the right i)
- Activate the plugin through the 'Plugins' menu in WordPress
- Find site-wide settings in Settings -> Two Cistron Hallmark ; observe your own user settings in the top-level bill of fare entry "Two Factor Auth".
If you want to add a section to the front end-finish of your site where users tin configure their 2-factor authentication settings, use this shortcode: [twofactor_user_settings]
-
What is two factor authentication (TFA / 2FA) ?
-
Basically, it's to practice with securing your logins, so that in that location's more than one link in the chain needing to be broken before an unwanted intruder can go in your website.
By default, your WordPress accounts are protected by merely one thing: your password. If that's broken, then everything'south wide open up.
"Two factor" means adding a 2d requirement. Usually, this is a code that comes to a device you ain (e.g. telephone, tablet) – so, someone can't get into your website without getting hold of your device. You tin can become a longer answer from Wikipedia.
Sometimes it is also called multi-factor authentication instead of two-factor – because someone could secure their systems with as many factors as they similar.
-
Why should I intendance?
-
Read this: https://www.wired.com/2012/08/apple-amazon-mat-honan-hacking/
-
How does two factor authentication (TFA / 2FA) work?
-
Since "two factor hallmark" just means "a second something is necessary to get in", this answer depends upon the detail set-up. In the most common case, a numeric code is shown on your phone, tablet or other device. This code be sent via an SMS; this then depends on the mobile phone network working. This plugin does not uses that method. Instead, it uses a standard mathematical algorithm to generate codes that are simply valid once each, or for only for 30 seconds (depending on which algorithm you choose). Your phone or tablet can know the code afterward it has been set up once (often, past just scanning a bar-code off the screen).
-
What do I need to ready on my telephone/tablet (etc.) in social club to generate the codes?
-
This depends on your particular make of telephone, and your preferences. Google have produced a popular app called "Google Authenticator", which is a preferred option for many people considering it is piece of cake to use and tin can be fix up via just scanning a bar code off your screen – follow this link, and ignore the showtime paragraph that is talking almost 2FA on your Google account (rather than being relevant to this plugin).
-
What if I do not accept a phone or tablet?
-
Many and various devices and programs can generate the codes. 1 choice is an add together-on for your web browser; for example, here are some apps and add-ons for Google Chrome. Wikipedia lists diverse programs for dissimilar computers.
-
I lost my device that has pass-codes – or, they don't work. What to practice?
-
If your laissez passer-lawmaking used to work, but no longer does, then bank check that the fourth dimension on your device that generates them is authentic.
If you cannot go in and need to disable two-gene authentication, and then add this to your wp-config.php file, using FTP or the file director in your hosting command panel:
define('TWO_FACTOR_DISABLE', true);Add it next to where whatever other line beginning with "ascertain" is.
Alternatively, if you accept FTP or cPanel admission to your web hosting space, y'all can de-activate the plugin; see this article.
-
Why does the plugin not support sending the 2-factor code past e-mail?
-
If someone has access to your email account, and so they can send a password-reset lawmaking there using the password-reset mechanisms congenital into WordPress. Therefore, if the two-factor lawmaking was as well sent in that location, then ability to read your email allows the breaking of both factors, and hence is no longer truly two factor authentication.
Some users might have two factor hallmark on their email account, but this is not knowable or controllable from within WordPress, and and then giving this pick to users ways that the ambassador cannot see or enforce 2-factor authentication. And fifty-fifty in this case, email is often sent between servers unencrypted, and and so is susceptible to man-in-the-middle attacks across the control of WordPress.
-
What are HOTP and TOTP?
-
These are the names of the two mathematical algorithms that are used to create the special codes. These are industry-standard algorithms, devised by expert cryptographers. HOTP is less pop, but the device that generates the codes does non need to know the correct time (instead, the codes are generated in a precise sequence). TOTP is much more pop, and generates codes that are but valid for 30 seconds (and and then your device needs to know the time). I'd recommend TOTP, every bit HOTP can be annoying if something causes the sequences to leave of sync.
-
What is the shortcode to use for front-end settings?
-
[twofactor_user_settings]
-
I deliberately entered a wrong countersign, and it let me login!
-
You have a password manager extension installed in your spider web browser, with the right password entered in it. It has automatically replaced your wrong countersign with the right one from its saved shop. This behaviour has been observed and confirmed past several users. You can verify it by using the web developer tools in your browser to look at the HTTP data sent to WordPress, and notice which countersign is actually in it. You lot can also open a fresh web browser with no such extension in information technology to re-test.
Note that the ii factor authentication plugin has no mechanism to compare or corroborate passwords; this is washed by WordPress cadre. If the wrong password is sent, and so this is handled by WordPress, and the login volition not proceed.
Payed only? Not ready for PHP-8 ? Asking for server features non being available?
Does the job without any troubles. Works with Google Authenticator and the Microsoft Authenticator as well. I besides recommend the plugins big brother: "UpdraftPlus - Rubber & restore"
I have used this product on a dozen of the websites I have congenital and take had positive results without exception. The plugin is maintained regularly and works with a diversity of Authenticator apps. Corking product, Highly recommended!
In the trial version I tried to make a specific user role to be requested (not forced) to setup his authenticator APP (i.e. FreeOTP), just it did non piece of work at all as the plugin did not exist at all. At least it did non practice any damage. Information technology was a compassion since this plugin was promising. UPDATE: After activating the plugin and put the shortcode [twofactor_user_settings] in the forepart of the website (in an Elementor cake), after a while a long text appeared in the front-cease where it should have been, but it did not recognize a the password of test-user I was testing. Overall, it seems to me also difficult to arrive working, and information technology is a pity since this plugin apperared to exist promising as others also. I gave up. And so far, I got something working only from "miniorange two factor authentication". Sometimes, while testing different plugins of this kind, I even ended locked out my website with no chance to log in once again. Luckly I was doing all testing on a staging website and I do recommend doing the same with these dangerous plugins (they either do not work at all – equally this i – or lock you out). For the paid version of this type of plugin, I also practice recommend to get a full endeavour-earlier-buy testing, otherwise practice forget about them.
First step goes already incorrect. Google Authenticator says "Invalid Barcode" when trying to enable the 2FA.
Install, actuate and setup all were like shooting fish in a barrel. We used Google Authenticator and this works well. The number of failed hacker login attempts has decreased dramatically.
Read all 70 reviews
"Two Gene Authentication" is open source software. The following people have contributed to this plugin.
Contributors
i.14.3 – 26/Jan/2022
- TWEAK: Change internal translation building and loading mechanism
- TWEAK: "https://" is not a translatable cord
- TWEAK: Load translations even if aborting due to incompatible PHP version
- TWEAK: Update updater libraries to current versions
1.fourteen.i – 08/Nov/2021
- REFACTOR: The constants SIMBA_TFA_PLUGIN_DIR and SIMBA_TFA_PLUGIN_URL have been abolished. If you had manus-coded any code that used them, then yous will want to review and test your customisations advisedly first. This applies for all refactoring items and internal changes mentioned below.
- REFACTOR: Internal plugin directory construction changed
- TWEAK: Fix a potential PHP coding notice in 1.13.0 when an administrator viewed a user's QR code
i.13.0 – 01/Nov/2021
- REFACTOR: Complete re-arrangement of all Premium lawmaking. If you lot had hand-coded whatsoever code which interacted with it, yous will want to review and test your customisations carefully first. This applies for all refactoring items and internal changes mentioned beneath.
- REFACTOR: Abolished the class Simba_TFA_Plugin_Admin_Dashboard_Integration
- REFACTOR: Moved some TOTP/HOTP-specific methods out of Simba_Two_Factor_Authentication into Simba_TFA_Provider_TOTP
- TWEAK: Class TFA_Frontend renamed to Simba_TFA_Frontend
- TWEAK: The constant SIMBA_TFA_PLUGIN_FILE is no longer used internally and has been abolished
- TWEAK: Move Premium plugin update loader into the main Premium class
- TWEAK: Factor out all Premium features into individual classes
- TWEAK: The method tfa_is_available_and_active() has been removed.
- TWEAK: The method Simba_TFA_Provider_TOTP::getPanicCodesString() has been renamed to Simba_TFA_Provider_TOTP::get_emergency_codes_as_string()
1.12.3 – 22/Oct/2021
- Gear up: Set the twofactor_user_qrcode shortcode in the Premium version
one.12.two – 21/Oct/2021
- Gear up: Preclude load-order related fatal error (regression since ane.12.0) on sites that did not have AUTH_KEY divers in wp-config.php
- TWEAK: Update updater library in Premium version to latest version
- TWEAK: Introduce templating method for better code system
1.12.1 – 18/Oct/2021
- REFACTOR: Continuing the major re-factor of the plugin's internal classes. If y'all had hand-written custom PHP lawmaking that hooks into whatsoever internal classes, you volition want to review your customisations carefully starting time.
- TWEAK: Update .pot file
ane.12.0 – 16/October/2021
- REFACTOR: Major re-factor of the plugin'due south internal classes. If y'all had hand-written custom PHP code that hooks into whatever internal classes, y'all will want to review your customisations carefully first.
- TWEAK: Harmonise wording on trusted devices label
- TWEAK: Remove redundant hex2bin compatibility for no-longer-supported PHP versions
ane.xi.0 – xiv/Sep/2021
- Characteristic: (Premium) Add new anti-bot feature for WooCommerce login forms: do not include the login class inside the page HTML (making them invisible to most bots), bringing it back via JavaScript. The feature needs to exist activated witin the plugin settings.
1.10.4 – 27/Jul/2021
- TWEAK: Fix a couple of minor visual regressions in the WooCommerce login course TFA field layout
one.ten.3 – 28/Jun/2021
- FIX: Incorrect object reference in Affiliate WP integration (regression in i.10.0)
1.10.two – 26/Jun/2021
- TWEAK: The script tfa_frontend.php now uses an external JavaScript file (better compatibility with with content security policies)
1.x.i – 25/Jun/2021
- FIX: Set up a bug in the Premium Elementor integration introduced in ane.ten.0.
ane.10.0 – 15/Jun/2021
- REFACTOR: Integrate the previously-separate WooCommerce/Affiliates-WP handlers in the main handler, eliminating redundant/duplicate code. Eliminate the internal concept of different form types by re-coding the few "type one"s as type twos. Separate login-course specific data from code.
1.9.6 – 04/Jun/2021
- Feature: Support bbPress login forms (Premium version)
1.9.5 – 26/May/2021
- TRANSLATIONS: Update bundled Spanish translation (es_ES) in Premium release
ane.9.4 – 25/May/2021
- FIX: Forbid an issue identifying the username field when on a page with both Affiliates WP login and registration forms, when the login grade displayed second
1.nine.three – 14/April/2021
- Ready: In the Premium version, when appending the TFA code to the countersign on third-party login forms with no directly back up, only usernames were accepted for the login (not electronic mail addresses)
1.9.2 – 20/Mar/2021
- TWEAK: When checking if a user has TFA enabled on a login page, perform the same sanitisation on the username as WP core, and then that if the user mis-types their username (which WP accepts) e.g. past prefixing a space, then they will nonetheless be asked for their TFA lawmaking (instead of jumping directly to an error for not supplying one)
- TRANSLATIONS: Added an Italian translation, thank you to Edoardo Di Leginio
one.9.1 – 15/Feb/2021
- TWEAK: Correct the "for" attribute of the "mark as trusted" text label on the WooCommerce login form
1.9.0 – 09/February/2021
- FEATURE: (Premium) If TFA is required for a user, and they have non yet set up it up, then strength them to be redirected to a configured URL
- TWEAK: Supervene upon the deprecated jQuery.click() and .change() methods
1.eight.8 – sixteen/Jan/2021
- TWEAK: Supercede the deprecated jQuery.unbind() and .focus() methods
- TWEAK: If the free version is active, then throw an fault if trying to actuate the Premium version, explaining what needs to be done
1.8.7 – 11/Jan/2021
- TWEAK: Update jQuery document prepare, click and submit styles to one not deprecated in jQuery 3.0, and supervene upon :first pseudo-selector with .first()
- TWEAK: At present marked as supporting PHP 5.vi+ (at present that PHP 8.0 is out)
- TWEAK: Update to the latest version of the bundled updater library (paid versions), which adds integration with WP 5.5+'south motorcar-updater
1.8.half dozen – 15/Sep/2020
- FEATURE: Add a 'TFA' column also to the Users screen in the WP network admin dashboard (multisite installs)
- TWEAK: Update the arranged updater library (paid versions) to the current release
1.8.five – 29/Aug/2020
- TWEAK: Fix the "for" attribute of the "trusted" text label on the WooCommerce login form
- TWEAK: If a website's wp-login.php is available under multiple hosts without CORS enabled between them, then AJAX calls would neglect; this is now resolved by using a relative URL instead
- TWEAK: Update bundled updater libraries on Premium version (improving compatibility with WP 5.5+'s update settings)
one.8.4 – 26/May/2020
- TWEAK: Updare .pot file; now both the first 2 parameters to _n() are too included in the aggregation procedure
1.8.2 – 23/May/2020
- Set: If the site owner was requiring a correct code to be supplied for activation, then this was too existence required for de-activation
- TWEAK: Introduce simbatfa_enforce_require_after_check filter, allowing developers to selectively disable the "require TFA after 10 days" bank check
- TWEAK: Update .pot file
1.eight.0 – eighteen/April/2020
- FEATURE: Add support in the paid version for Elementor login forms
- TWEAK: Updater in paid version now will brand checks on availability without needing login
- TWEAK: Update updater class to electric current release
1.seven.iv – 19/Mar/2020
- TWEAK: Adjust how the trusted field is referenced from JavaScript, fixing IE11 compatibility
- TWEAK: Introduce the filter simba_tfa_required_for_user
1.vii.3 – 03/Mar/2020
- TWEAK: Provide not-plural culling for trusted device phrase
- TWEAK: Marker as supporting WP 5.4
1.7.2 – 13/Feb/2020
- TWEAK: Update message about what to exercise with translations
ane.7.1 – xiv/Jan/2020
- Fix: Missing file in i.vii.0 (complimentary) release
ane.7.0 – 14/Jan/2020
- Feature: (Premium version): Add an optional TFA section to the WooCommerce account details section in "My Account"
- TWEAK: Fix div tag balancing issue in settings output
- TWEAK: Update WooCommerce integration to adjust to DOM changes in WooCommerce iii.viii
- TWEAK: Update .pot file
1.6.iv – 12/Nov/2019
- TWEAK: On wp-login.php on WordPress 5.3, the password field was not hiding when the TFA field opened
- TWEAK: Update .pot file
- TWEAK: Add data-lpignore attribute to TFA field to indicate to LastPass that it is non a password field
one.6.3 – 18/Oct/2019
- Fix: The 'trusted users' option display in the settings defaulted to showing as enabled, whereas in fact the default setting is disabled
- TWEAK: Mark equally compatible with WP 5.three
1.six.2 – xi/Sep/2019
- Prepare: On multisites, assistants of site users who were not nowadays on the main site was not possible
- TWEAK: Introduce the WP action simba_tfa_activation_status_saved to let developers to answer to activation status changes
- TWEAK: Update updater class to 1.viii series
1.half dozen.i – 10/Aug/2019
- TWEAK: Response to an endeavor to plough TFA on can at present include an "error" aspect if the attempt failed due to failure to supply the electric current lawmaking
1.6.0 – 08/Aug/2019
- Characteristic: (Premium version) By using the parameter fashion="require_current" with the shortcode twofactor_user_settings_enabled, the user will only be able to activate TFA if they enter the current TFA lawmaking
- TWEAK: Remove the wrong suffix "(Premium)" (double-suffix in the actual Premium version) that appeared in the plugin championship in ane.5.half-dozen
i.5.6 – 06/Aug/2019
- TWEAK: Permit customisation of a item message via a filter simbatfa_message_you_should_verify
- TWEAK: Replace "eachother" with "each other"
1.5.5 – 30/Jul/2019
- TWEAK: Strength a global context when creating the initial Simba_Two_Factor_Authentication object, to piece of work around direct accesses from components that exercise not set up the scope correctly
1.5.4 – 17/Jul/2019
- Feature: (Premium version) – allow the site ambassador to forbid users who take compulsory TFA to turn information technology off (supplementing the boosted adequacy to prevent them logging in)
1.5.3 – 22/Jun/2019
- TWEAK: When using your terminal emergency lawmaking (Premium version), and viewing your settings (which regenerated new ones), then if you did not follow the communication to reset your prviate key, you would go the same codes as before. This might be idea undesirable (though is not a security flaw, as the emergency codes are no more guessable the 2nd time effectually than the beginning). This behaviour has at present been inverse.
1.v.ii – 08/Jun/2019
- TWEAK: When php-mcrypt was not installed, pressing the "Reset private fundamental" link in a user's settings would cause an unnecessary PHP observe, and brandish a incorrect "current code" for a few seconds.
ane.five.1 – 05/May/2019
- Characteristic: Support any login course (Premium version) via appending the TFA code onto the cease of the countersign. This allows support even of login forms coded in a way that make integrations (that aren't hacks or inordinate amounts of piece of work-around lawmaking) impossible (e.k. PeepSo)
- TWEAK: Minor wording tweak in the explanation of how TOTP works.
ane.4.12 – eighteen/April/2019
- TWEAK: Add a filter simba_tfa_localisation_strings allowing further customisation of forepart-end strings
- TWEAK: Add an extra instructional message in the "Make two cistron authentication compulsory" section (Premium) to explain how to cope with existing users
- TWEAK: Cope with the user entering spaces in their two-gene code (TOTP protocol codes are numbers only, but some apps patently brandish formatting and users are not aware)
- TWEAK: Mark as supporting WP five.2
ane.4.eleven – 08/Mar/2019
- FIX: On multisites, the user search should search on all sites, not just the principal one
ane.4.10 – 01/Mar/2019
- TWEAK: Introduce a filter, simba_tfa_management_capability, assuasive the WP capability (default: manage_options) required by a user to manage the plugin to be inverse. (Be conscientious – giving the ability to manage could potentially mean the ability to lock whatever user out).
1.4.9 – 20/Feb/2019
- SECURITY: The security fix in version 1.4.seven was faulty and failed to completely fix the problem; it is at present resolved in this release. Our apologies for the double update.
1.four.8 – 16/Feb/2019
- FIX: On some multisite setups, the link to the site-wide administration settings went to the incorrect place
ane.4.7 – 06/Feb/2019
- SECURITY: If a user's WordPress account username was in the form of an email accost, and if their actual business relationship email address was something different, and TFA was set upwardly on that account, and used the "username" (that looked like an email accost) to login, then TFA controls upon login on that account would be ineffective. Other accounts were not affected (regardless of whether you login past email or not). This vulnerability was inherited from the original "2 Factor Auth" plugin that this plugin was forked from, and then is present in all versions before this i.
1.4.6 – 05/Feb/2019
- FIX: When displaying a user's trusted devices in the admin page, the time that a device was trusted until was not shown correctly (instead, it showed the current time)
- Gear up: Removing the first trusted device in a list did not e'er work
- TWEAK: Display "(none)" when there are no trusted devices
1.4.4 – 04/Feb/2019
- FEATURE: Trusted devices are now listed in the user'southward admin folio, assuasive them to run across and remove trust from their devices.
- TWEAK: Updated .pot file
1.iv.iii – 28/January/2019
- Fix: The "Trusted devices" functionality (Premium) checkbox was not actualization when activated
- TWEAK: Add together a missing translation domain to a phrase
1.four.1 – 25/January/2019
- FEATURE: Trusted devices: A site possessor tin can now cull to let particular user levels (e.k. admins, editors) to mark devices as 'trusted' and thereby exempt from needing to enter a TFA code for a chosen number of days. This feature is off by default and requires https (i.eastward. SSL) on the login form and cookies to be kept in the trusted device.
- FIX: Fix a regression in 1.four.0 whereby when a site owner viewed another user'due south current lawmaking, it could subsequently self-update with the wrong user's value
- TWEAK: Add the robustness in parsing broken JSON present on the standard WP login form to other login forms
- TWEAK: Diverse internal code documentation improvements
- TWEAK: Suppress mcrypt deprecation notices in places where we would use an alternative if information technology was not present
- TWEAK: Bumped the back up requirement up to WP iii.iv. I'm not enlightened of anything done to break it on three.3, but this is the official requirement (it's very difficult to test sometime WP versions as they don't run on mod webserver stacks)
one.four.0 – 24/Jan/2019
- Characteristic: Where the electric current OTP code is displayed (during setup), this will at present cocky-update automatically (i.e. without needing a manual printing on the "update" link).
- TWEAK: Various improvements to the layout and text of the setup page to assist make the process more than understandable
- TWEAK: The current code is shown next to the UI pick for enabling TFA
- TWEAK: Prevent a PHP notice if AUTH_KEY was not divers (on some very onetime WP installs)
i.three.xiii – 18/December/2018
- SECURITY: Fix a logged-in CSRF vulnerability reported by Martijn Korse (www.bitnesswise.com). Due to a missing nonce bank check, if an attacker was able to persuade a personally-targetted victim who was currently logged in to their WordPress business relationship to visit a personally-crafted (for the individual victim) page in the same browser session, and so the attacker would exist able to de-activate two-factor hallmark for the victim on that WordPress site (thus leaving the targetted business relationship protected past the user's countersign, just non by a second cistron – the absence of a request for a TFA code would be apparent on the user's next login). This vulnerability was inherited from the original "Ii Gene Auth" plugin that this plugin was forked from, and and then is present in all versions before this one.
- TWEAK: Some modest code-tidying
- TWEAK: Update bundled Premium updater library to current version (1.five.10)
1.three.12 – xiv/Dec/2018
- TWEAK: Prevent a PHP debugging discover when $pagenow is not prepare
i.iii.11 – 04/December/2018
- Feature: Add a 'TFA' column on the Users screen in the WP admin dashboard to display TFA status, thanks to Enrico Sorcinelli.
i.iii.10 – 30/Nov/2018
- FIX: TFA codes were not being requested on the login form on a WooCommerce dedicated order payment page (i.e. /checkout/lodge-pay/123456/?pay_for_order=truthful&fundamental=wc_order_blahblahblah) (meaning that if a user had TFA activated, login would fail).
- TWEAK: Foreclose a PHP find if AUTH_SALT was non defined (on some very old WP installs)
ane.3.9 – 30/Oct/2018
- SECURITY: If you lot were non using the recommended selection of requiring 2FA for XMLRPC requests, then an attacker could potentially also featherbed requirements for 2FA on ordinary logins (i.east. just need the countersign). Such users will want to immediately update, though we recommend that all users practice. This vulnerability was inherited from the original "Two Factor Auth" plugin that this plugin was forked from, and so is present in all versions before this 1.
i.3.viii – 25/October/2018
- TWEAK: Update the updater class in the Premium version to the electric current release (1.5.6)
1.iii.7 – 15/October/2018
- TWEAK: Endeavor to mitigate plugins on the login page which cause JavaScript exceptions by enqueing our scripts earlier.
1.3.6 – 04/Oct/2018
- TWEAK: Add together aspect autocomplete="off" on the WooCommerce login form TFA field (was already present for regular WP login form)
- TRANSLATION: Added Portuguese (Brazilian) translation, courtesy of Dino Marchiori
one.3.5 – 02/October/2018
- TWEAK: Some code-styling consistency clean-ups
- TWEAK: Allow one more than window's tolerance by default for codes from devices running fast
1.three.four – xi/Sep/2018
- FIX: Sometimes a TML widget login class could fail to work because of a inverse/unexpected DOM tree
- FIX: Some further breakage in TML had occurred, causing login buttons to require to be pressed twice
1.iii.3 – 31/Jul/2018
- FIX: Restore support for "Theme My Login", which had been cleaved by unannounced changes in TML 7.x
- TRANSLATIONS: Update .pot file
1.3.2 – 31/May/2018
- TWEAK: Add together the simbatfa_check_tfa_requirements_ajax_response and simbatfa_verify_code_and_user_result filters to allow over-riding of the response to the "TFA required?" question and the TFA bank check itself by developers
1.iii.1 – 25/May/2018
- FIX: The WooCommerce 3.iii+ login form was requiring two clicks on the 'Log In' push
- TWEAK: The progress spinner had disappeared on WooCommerce 3.3+
i.3.0 – 05/April/2018
- FEATURE: (Premium version) Integration with the WP-Members login form, https://wordpress.org/plugins/wp-members/ . N.B. WP-Members does not laissez passer on the real error message upon a login failure, but displays its ain hard-coded message that the username/password were wrong; and then you'll see this even if it was actually the TFA code that was wrong.
- TWEAK: Change the permission check for editing other users (Premium version) to edit_users (instead of the previous update_plugins, intended but as a proxy for "is an admin")
- TWEAK: End using the deprecated jQuery.parseJSON method
- TWEAK: Change a string that was not in a translatable class
- TWEAK: Update the updater class in the Premium version to the current release (1.5.1)
1.2.35 – 28/November/2017
- TWEAK: Upon front-end settings save, do jQuery(document).trigger('tfa_settings_saved'), allowing the user to reply to the action (e.g. reload page)
- TWEAK: Suppress mcrypt deprecation notices on PHP seven.ane (nosotros already know it is deprecated, and already use openssl if information technology is not installed)
one.2.34 – 08/Nov/2017
- TWEAK: Remove calls to the deprecated screen_icon() role
- TWEAK: Remove some unnecessary bundled translation files
- TWEAK: Add together some translation files not previously included in the Premium version
- TWEAK: Update bundled Premium updater library to current (one.5.0)
one.ii.33 – 09/Oct/2017
- Fix: The available/required settings for super-admins on multisite installs were non saving (Premium feature)
- FIX: When the admin fetched another user'southward current QR code, it embedded the wrong username (which was a cosmetic issue only – the code itself was right) (Premium characteristic)
1.2.32 – 06/Oct/2017
- TWEAK: Update bundled updater in Premium to latest version (1.4.eight)
1.two.31 – 05/Oct/2017
- FEATURE: (Relevant to Premium version): Automatically generate new emergency codes when they run out, including upon view of settings if in that location are none (due east.g. on upgrade from free to Premium)
- TWEAK: Code-styling consistency tweaks
1.2.30 – eighteen/Sep/2017
- FIX: TML shortcode forms were not working properly for not-TFA users
1.2.29 – 16/Sep/2017
- Set up: Prevent double-show of TFA field on TML default login folio (regression)
- Gear up: Restore functionality on TML shortcode forms (regression, probable due to changes in TML)
- TWEAK: Restore the spinner to proper size on all forms
- TWEAK: A few very small-scale code fashion clean-ups
1.2.27 – 29/Aug/2017
- TWEAK: Add together the new 'PHP Requires' header to readme.txt
- TWEAK: Correct a couple of wrong translation domain references
1.2.26 – 08/Aug/2017
- FIX: Do not request TFA code on TML reset password form (regression, likely due to changes in TML)
- APOLOGIES: 1.2.25 was a faulty release that would cake logins. You should immediately update.
1.two.24 – 05/Aug/2017
- TWEAK: Update to the latest version of the updater library (Premium)
1.2.23 – 15/Jun/2017
- TWEAK: Allow admins to reset users' individual keys (Premium)
i.two.22 – 23/May/2017
- TWEAK: Update updater library to current version (Premium)
- TWEAK: Use college-quality spinner paradigm
- COMPATIBILITY: Marker as compatible with WP 4.8
one.2.21 – 22/February/2017
- TWEAK: Update jquery-qrcode library to latest release (0.fourteen.0)
- TWEAK: Explicitly encode spaces in WordPress usernames (apparently resolves a problem with a detail iPhone app)
i.two.20 – 17/February/2017
- TWEAK: Work effectually a bug seen with strlen() on 1 particular PHP install
- FIX: The line purporting to bear witness the electric current UTC time was in fact taking your WordPress timezone into account. It has now been adjusted to show both to avert ambiguity.
- FIX: 1.ii.18 used a PHP five.4+ just part, whereas nosotros support PHP five.3+
1.ii.17 – 09/February/2017
- FIX: Set support for login widgets from Theme My Login
1.2.xvi – 30/Jan/2016
- Ready: Fix result whereby if you lot were already logged in and managed to visit a login form, you lot would non be asked for a TFA code
1.2.xv – 23/Jan/2017
- FEATURE: Add together back up for login widgets from Theme My Login
- UPDATER: (Premium version): update to the latest updater class, including the new ability to automatically update
1.two.14 – 02/January/2017
- TWEAK: Add missing internationalisation headers to the main plugin file
1.2.thirteen – 31/Aug/2016
- TWEAK: Internationalisation implementation was non previously compatible with wordpress.org's translation system
one.2.12 – 20/May/2016
- Feature: Compatibility with https://wordpress.org/plugins/use-ambassador-password/ – when TFA is enabled on an account, the TFA credentials of the user whose password was supplied are allowed (and required)
1.2.11 – eighteen/May/2016
- TWEAK: Update bundled select2 to version 4.0.2
- Prepare: If the [twofactor_user_qrcode] shortcode (Premium version) was used without other short-codes, so the code would not display
i.two.x – 31/Mar/2016
- TWEAK: Prefer openssl, if present, to the deprecated mcrypt. Annotation that if you migrate a site from a server without openssl to a server without mcrypt, and then because of mcrypt's non-compliant padding, y'all volition need to either install php-mcrypt on the new server, or disable TFA (via define('TWO_FACTOR_DISABLE', true); in your wp-config.php) to allow users to be able to log in. This also applies if the source site did have openssl, merely for users who hadn't logged in since installing this update.
- TWEAK: Make the $simba_two_factor_authentication_premium object globally available
- COMPATIBILITY: Mark every bit tested on WP 4.5
1.2.8 – 12/December/2015
- FEATURE: Add support for the Affiliates-WP login form
- TWEAK: Defeat WooCommerce loading an one-time version of the select2 script onto the TFA settings folio, and breaking the user selector (should work this fourth dimension)
1.two.vi – 11/Nov/2015
- TWEAK: Defeat WooCommerce loading an one-time version of the select2 script onto the TFA settings folio, and breaking the user selector
- TWEAK: Tested on WordPress 4.4
- TWEAK: Utilise h1 for heading style on admin page, not h2
- FIX: The "Y'all'll need to utilize TFA to login in future" link for users for whom TFA is compulsory (Premium) was to the wrong page
ane.2.4 – 09/November/2015
- TWEAK: Make window settings filterable
1.2.three – nineteen/Oct/2015
- FIX: Set up bug in one.2.2 that could lock out users without TFA settings
one.ii.2 – 16/October/2015
- TWEAK: Brandish dashboard find if TWO_FACTOR_DISABLE is defined in wp-config.php, to preclude time wasted wondering why nothing is happening
i.two.ane – 08/Oct/2015
- Characteristic: (Premium version) – Require users (of configured roles) to use TFA (optionally after a configurable amount of time)
1.one.21 – 25/Aug/2015
- TRANSLATIONS: Translation files can now be used (translators welcome!)
- TRANSLATION: Swedish translation added, courtesy of Bo Sving
1.1.19 – 20/Aug/2015
- TWEAK: Remove a pointless nonce bank check
1.ane.18 – 01/Aug/2015
- COMPATIBILITY: Tested with WP 4.3 (RC1) and WooCommerce 2.4 (RC1) – no problems found (i.e. previous releases believed to be already compatible)
- Ready: When the admin is showing codes for other users, QR codes were not displaying correctly since 1.1.thirteen
1.ane.17 – 22/May/2015
- TWEAK: Innovate convenience method for developers wanting to verify that TFA is active (Premium)
- Set up: Fix operation of [twofactor_conditional] shortcode (Premium)
- FIX: Set fatal error introduced in convenience method in 1.i.16
1.ane.15 – 13/May/2015
- Fix: Fix conflict with 'reset password' class with "Theme My Login" plugin
1.1.14 – 12/May/2015
- Prepare: Add TFA support to the WooCommerce login-on-checkout course (previously, TFA-enabled users could non log in using it)
1.ane.13 – 11/May/2015
- TWEAK: Use jquery-qrcode to generate QR codes, replacing external dependency on Google
- TWEAK: Update arranged select2 library to iv.0.0 release (was rc2)
ane.1.12 – 22/April/2015
- FIX: Gear up corner-case where the user's login looked like an e-mail address, merely wasn't the account address. In this case, a OTP countersign was always requested.
- Fix: When the username does not exist, front-end should not request TFA code.
ane.1.11 – 21/Apr/2015
- TWEAK: Prevent PHP notice if combining with bbPress
- TWEAK: Added more console logging if TFA AJAX asking fails
- TWEAK: Add some measures to overcome extraneous PHP output breaking the AJAX conversation (eastward.g. when using strict debugging)
1.1.10 – twenty/Apr/2015
- SECURITY: Fix possible non-persistent XSS issue in admin expanse (https://blog.sucuri.net/2015/04/security-informational-xss-vulnerability-affecting-multiple-wordpress-plugins.html)
- FIX: Don't get involved on "lost password" forms (intermittent issue with "Theme My Login")
one.1.9 – 15/April/2015
- TESTING: Tested with "Theme My Login" – https://wordpress.org/plugins/theme-my-login/ – no issues
- TWEAK: Practice a little bit of status logging to the browser'south developer console on login forms, to assist debugging any issues
- TWEAK: Add a spinner on login forms whilst TFA status is being checked (WP iii.viii+)
- TWEAK: Make sure that scripts are versionned, to prevent updates not existence immediately effective
- TWEAK: Make sure OTP field on WooCommerce login form receives focus automatically
1.i.viii – 14/April/2015
- FIX: Fix an issue on sites that forced SSL admission to admin area, but not to front end-stop, whereby AJAX functions could fail (e.one thousand. showing latest lawmaking)
- FIX: Version number was not shown correctly in admin screen since 1.1.five
- TWEAK: Show proper plugin URI
i.ane.7 – ten/April/2015
- Set: Prepare plugin compatibility with PHP 5.six
- Set: TFA was always made active on XMLRPC, even when the user turned it off
1.one.half-dozen – 09/Apr/2015
- TWEAK: Change various wordings to make things clearer for new-comers to two-factor authentication.
one.1.5 – 07/April/2015
- FEATURE: Admin users (Premium version) can show codes belonging to other users, and activate or de-activate TFA for other users.
- PREMIUM: Premium version has now been released: https://www.simbahosting.co.britain/s3/product/two-factor-authentication/. Features emergency codes, personal support, and more than short-codes allowing y'all to custom-pattern your own front-end page for users.
- TWEAK: Premium version now contains support link to the proper identify (not to wordpress.org's free forum)
- TWEAK: Added a constant, TWO_FACTOR_DISABLE. Define this in your wp-config.php to disable all TFA requirements.
- Ready: Fix a bug introduced in version 1.i.2 that could prevent logins on SSL-enabled sites on the WooCommerce class when not accessed over SSL
i.1.3 – 04/Apr/2015
- TWEAK: Provide "Settings saved" notice when user's settings are saved in the admin area (otherwise the user may exist wondering).
1.1.ii – 03/April/2015
- FIX: Include blockUI JavaScript (the lack of which acquired front-end options non to save if you lot did not have WooCommerce or another plugin that already used blockUI installed)
- FEATURE: Don't show anything on the WooCommerce login grade unless user is using 2FA (i.e. behave like WP login form)
- FEATURE: Added ix new shortcodes for custom-designed forepart-stop screens (Premium – forthcoming)
i.1.1 – 30/Mar/2015
- Back up added for multisite installs. (Plugin should exist network-activated).
- Support added for super-admin role (information technology's not a normal WP office internally, so needs custom handling)
- Tested + compatible on upcoming WP 4.two (tested on Beta 3)
- Re-add pick to crave 2FA over XMLRPC (without specific code, XMLRPC clients don't/tin can't apply 2FA – simply requiring it effectively blocks hackers who want to crack your countersign past using this weakness in XMLRPC)
1.0 – 20/Mar/2015
- First version, forked from Oskar Hane'due south https://wordpress.org/plugins/two-gene-auth/
- Support for e-mail "two-factor" removed (email isn't really a second factor, unless you lot take multiple electronic mail accounts and guard where your "lost login" emails get to)
- WooCommerce support added to the primary plugin. Load WooCommerce JavaScript merely on pages where it is needed.
- Use AJAX to refresh current lawmaking (rather than reloading the whole page)
- Added WordPress nonces and user permission checks in relevant places
- Shortcode twofactor_user_settings added, for front-terminate settings
- User interface simplified/de-cluttered
Source: https://wordpress.org/plugins/two-factor-authentication/
0 Response to "Authentication Failed: Please Try Again Later or Use Public Search Instead."
Post a Comment